Emergency management: mitigating risks and streamlining response.

In a world of uncertainty, effective emergency management is critical to mitigating risk and streamlining response to unexpected situations. Whether it’s natural disasters, technical malfunctions, or other unforeseen events, well-designed emergency management can protect businesses, communities, and even individuals from serious consequences. In this blog post, we’ll explain the importance of emergency management and how it can help mitigate risks and streamline responses.
Why is emergency management important?
There are many reasons for effective emergency management. Not only does it help minimize human suffering and financial losses, but it can also protect the reputation of a company or organization. A poor response to an emergency can have far-reaching negative effects, from lost revenue to litigation. Well-planned emergency management can help mitigate these risks.
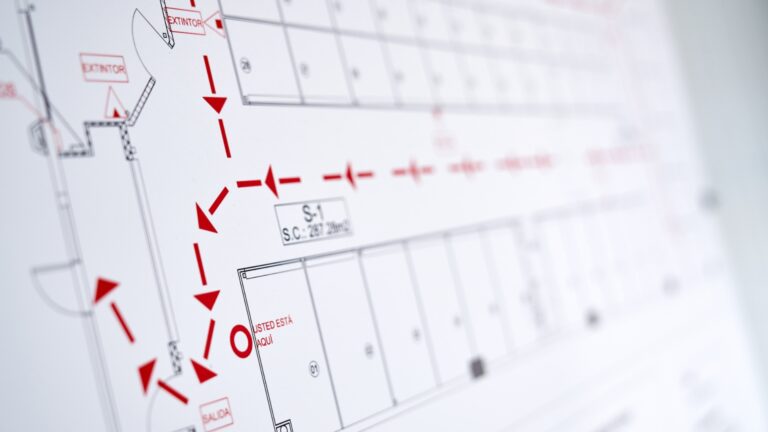
Emergency management begins with a comprehensive risk analysis. Companies and organizations should identify which potential emergencies could jeopardize their operations. These include natural disasters such as floods, earthquakes and storms, as well as technical failures, data loss and cyber-attacks. Once risks are identified, steps can be taken to mitigate those risks. This may include improving building security, implementing backup systems, or training employees in emergency procedures.
A well-designed emergency management system also includes clear procedures and plans that will be implemented in the event of an emergency. This allows for a streamlined and coordinated response to the event. Employees should know exactly what to do, who is responsible, and how to communicate during the emergency. Quick and accurate responses can significantly limit the impact of the emergency.
Emergency management is a topic of great importance that not only concerns companies. That’s why we recommend you take a look at our MobiCall alarm server. A well thought-out emergency management can help to reduce the risk and optimize the response in critical situations. Our multimedia alerting and notification helps you prepare and prevent, and plays a key role in mitigating risk and simplifying response.
If you would like more information on this topic or need assistance in developing an emergency response plan for your organization, please do not hesitate to contact us. We would be happy to assist you.